Email compromise: How to Protect Your Business from BEC Attacks
An email attack is one of the favorite ways for cybercriminals to compromise company information. In 2022 alone, 60% of companies in Russia faced a Business Email Compromise (BEC) attack, with the average amount of damage doubling compared to the previous year, reaching up to 4 million rubles. Alexey Drozd, the head of the information security department at SurchInform, explains why these attacks are so widespread and offers guidance on how to protect against them.
Cybercriminals' objectives and business implications
A BEC attack is a social engineering-based attack that compromises a corporate email account. Before executing such an attack, cybercriminals gather information about the potential victim and the victim's company. It is often easy for attackers to find and use the obtained information against the victim and their colleagues, as many employees openly share personal details on blogs and social networks, such as their workplace, vacations, and more. However, cybercriminals are primarily interested in obtaining information about the management, such as emails, business trip schedules, payment details, and company invoices. This makes it easier for cybercriminals to deceive, for example, the chief accountant and get money transferred to a "fake" account.
Attackers can carry out these attacks by hacking into a company's email system or the emails of its business partners. After gaining access to the correspondence, they can impersonate the individuals involved and utilize the gathered information for their own malicious purposes. In some cases, cybercriminals do not directly write from hacked email accounts; instead, they register a phishing domain that closely resembles the original one and continue the correspondence from there. For example, they may use "@serchinform.ru" instead of "@searchinform.ru." This method of spoofing is called typosquatting, where the name of a company's domain is deliberately misspelled.
For example, in 2019, a Chinese venture capital fund lost $1 million in a BEC attack when it intended to invest in an Israeli startup. The cybercriminals intercepted the correspondence between the two firms and initiated dialogue with the fund on behalf of the startup, and vice versa. To execute this attack, the attackers used fake domains that differed from the real ones by only one letter "s", it was added to the end of the domain name.
The popularity of these attacks can be attributed to their speed and ease of execution. A recent study by Microsoft Security Intelligence revealed that an attacker can spend as little as two hours, from first login to deleting a sent message. During this short timeframe, cybercriminals can obtain a substantial monetary gain or achieve other objectives, such as gaining access to infrastructure or sensitive information. In some cases, attackers use BEC attacks to obtain physical assets, such as merchandise.
An attempted attack targeted a sugar supplier, where the intruder's email correspondence requested a truckload of sugar to be sent to a specified address on credit. However, the employee who received the email noticed an error in the email address — the domain name contained an extra letter. The specialist contacted the firm to verify whether the sender was an employee, but the response confirmed otherwise. Consequently, the cybercriminal failed to receive the free product.
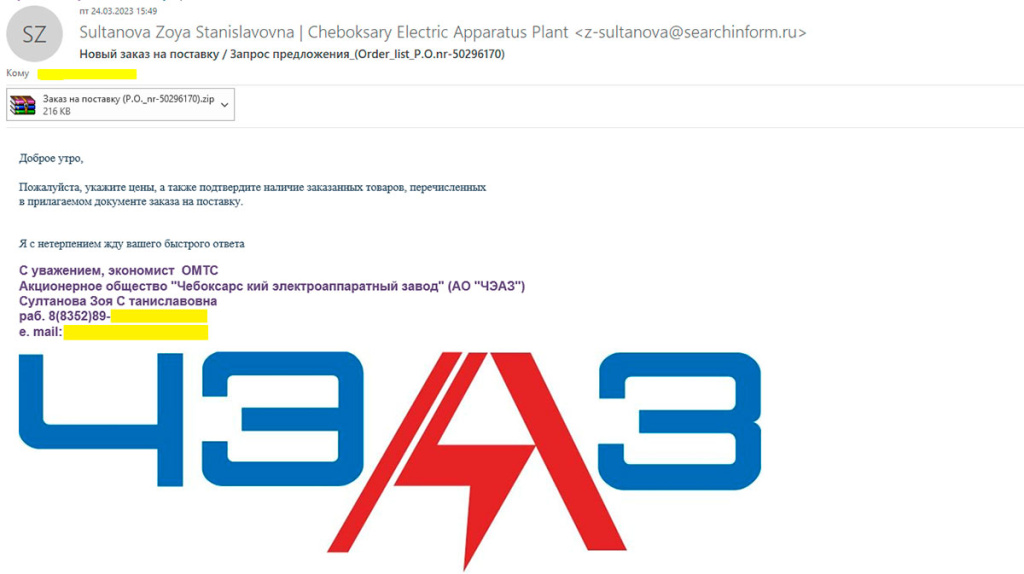
Recently, one of our company's departments received a letter requesting the delivery of goods. Since we hadn't been in contact with the other party, we couldn't determine the exact purpose of the email. However, in theory, if we were selling the requested goods, the email could have been of interest.
In such cases, we should carefully check the sender's email address. In our case, there are discrepancies between the name of the domain and the sender's company. However, this may have been done just to attract attention, as the signature contains an existing email address with the correct domain. Additionally, there are a few typos in the letter, which is often indicative of fake emails. The phone number provided in the signature is not publicly available, but upon comparing it with the numbers on the company's website, we can conclude that it is close to the genuine contact information.
If you receive a similar letter from a business partner who typically communicates differently, it is advisable to directly contact their supervisor or secretary to confirm its authenticity. Calling the head office to inquire whether the employee sent the letter can also provide further clarification.
Other Forms of BEC Attacks
Emails are not the only platforms targeted for these attacks; they can serve as one of the stages. Criminals have recently started exploiting virtual meeting platforms like Zoom to convince employees to transfer funds or disclose sensitive information. These tactics can include techniques like dipshake and, in some cases, video spoofing.
For example, an attacker might gain access to an executive's inbox and send employees an invitation to a video conference call. During the call, the attacker spoofs their identity and claims to have technical issues with the connection or microphone. They then introduce the topic of transferring funds and provide instructions on where to send them.
Although such incidents have been reported in the United States, with the advancement of technology, including the creation of deepfakes, and the decreasing cost of implementation, hackers in other countries may become interested in adopting this method.
Preventing BEC Attacks
Since BEC attacks are based on social engineering, comprehensive protection measures are necessary. The first step is to provide cyber literacy training for employees, followed by implementing security solutions and introducing internal regulations.
Employee training in cyber literacy is a crucial aspect of security. Without proper training, employees may fail to recognize suspicious emails, resulting in significant financial losses for the company. You can conduct in-house training sessions, educating employees about phishing emails, BEC attacks, how to differentiate between fake and genuine emails, and then provide practical training by simulating fake emails. If your organization lacks the resources for internal training, it is better to seek assistance from professionals. For instance, our company has been providing cyber literacy training for businesses, state institutions, and municipalities for the past three years. Distributing easy-to-understand memos can also help prevent various threats, such as phishing emails, weak passwords, and unauthorized program installations.
The second step involves employing email security tools. These software solutions combat external threats and can include Next-Generation Firewalls (NGFW) to prevent network attacks, anti-spam measures to reduce phishing attempts, and the implementation of SPF, DKIM, and DMARC protocols for sender authentication.
Some tools designed to protect against insider threats can also help mitigate this problem. For example, our Data Loss Prevention (DLP) solution now includes functionality that distinguishes between genuine and fake domains.
Additionally, internal regulations should be established, requiring employees to verify payment requests received via email through alternate channels or implement multi-factor authentication for critical actions.
The number of BEC attacks continues to rise, with a 15% increase in incidents reported in Russia in 2022 compared to the previous year. This indicates the urgent need for companies to prioritize robust protection measures, thus reducing the risks and consequences associated with corporate email compromise.

